About 7 min read
LYNX: why encryption, shared bookmarks, and human-led AI matter for ops teams
Privacy-first bookmarks, notes, and chat—how we shipped trustworthy crypto with AI acceleration and human review.
Most teams do not lack tools—they lack a calm home base. Links scatter across browsers, notes live in five apps, and “quick questions” become endless threads. LYNX (live at lynxdash.com) answers that with a single privacy-first dashboard: organize bookmarks by category, author encrypted notes, chat in real time with disposable keys, and personalize the experience—without selling your attention or your data.
What LYNX delivers
The product story on lynxdash.com is explicit: your secure digital dashboard—not a file dump, not another social network. Smart bookmarks with colors, icons, and categories put shared infrastructure (hosting panels, cloud consoles, status pages) one click away. Rich-text encrypted notes use your personal cipher so only you can read them. A weather widget and customizable layout keep the surface friendly, while the security model stays enterprise-minded: multi-factor authentication, bcrypt-hashed passwords with strength rules, rate limiting, CSRF and XSS protections, and strict security headers.
The differentiator for day-to-day operations is Secure Ephemeral Chat: WebSocket-based messaging with AES-256-GCM encryption, disposable cipher keys per session, and deliberate disposal of messages during sessions so sensitive coordination does not fossilize in a searchable archive by default. Participants can terminate a session and wipe data for everyone—valuable when credentials, customer context, or remediation steps should not linger.
Why privacy and encryption are non-negotiable
Shared bookmarks and instant messaging are how modern teams move. Independent communication surveys from 2024 found that roughly one in four professionals pointed to online chat tools as their primary channel with coworkers—while email still led for about three in ten respondents—illustrating how fragmented “where work happens” has become. Project-management tools and other channels divided the rest, which helps explain why people constantly context-switch.
Zoom’s global collaboration research has highlighted another pressure point: organizations where employees rely on many distinct collaboration applications—often ten or more—report disproportionately more time lost resolving coordination breakdowns than peers with tighter toolchains. Microsoft’s annual Work Trend Index releases have similarly tracked explosive use of AI assistants among knowledge workers, with recent waves of surveys describing roughly three in four such workers engaging AI for everyday tasks—useful context when you ask whether automated help belongs inside a secure workspace instead of scattered across unvetted extensions.
Those patterns explain why LYNX treats both shared resources (bookmarks your whole team relies on) and private channels (ephemeral chat, encrypted notes) as first-class. When a large share of the week is coordination, the cost of “just paste it in the group chat” becomes compliance risk, customer trust, and burnout. End-to-end encryption and disposal are not theatrics—they bound where secrets can leak.
The Lynx feature set doubles down on that posture: chat supports encrypted file handoffs during live sessions—files are removed from the server side once retrieved, aligning with the same ephemeral mindset as the messages. Notes include fast search across categories so operators can pull runbooks or customer nuances without exporting plaintext to a third-party memo app. Multi-factor authentication and brute-force protections round out the account edge—because the prettiest dashboard is worthless if the login path is soft.
Where AI helped—and where humans stayed in charge
Building LYNX was not “prompt once and ship.” Large language models excelled at boilerplate acceleration: translating dense API docs into scaffolding, exploring UI variations, drafting test matrices, and surfacing edge cases in authentication flows. That speed matters when you are iterating on encrypted transports and session lifecycle rules—especially when WebSocket paths, cipher resets, and disposal hooks must stay synchronized.
Human-guided prompting mattered most when requirements were subjective: how aggressive to be with session teardown, how much friction to add before deleting chat content, and how to phrase warnings so non-experts understand risk without panic. We iterated prompts the same way we iterate UX copy—tight feedback loops, side-by-side review of model output against security requirements, and refusal to accept “mostly right” crypto helpers.
What AI did not replace was judgment: threat modeling, key-handling policy, acceptable retention for disposed chat data, and UX trade-offs that favor clarity over cleverness. Human reviewers enforced those decisions in code review and QA. Industry-wide, employer surveys in 2024 continued to show rapid adoption of AI assistants among knowledge workers—the highest-performing teams still paired automation with explicit review gates for anything customer-facing or compliance-adjacent. We ran LYNX the same way: AI as a multiplier, humans as the approval surface for anything that touched cryptography or customer trust.
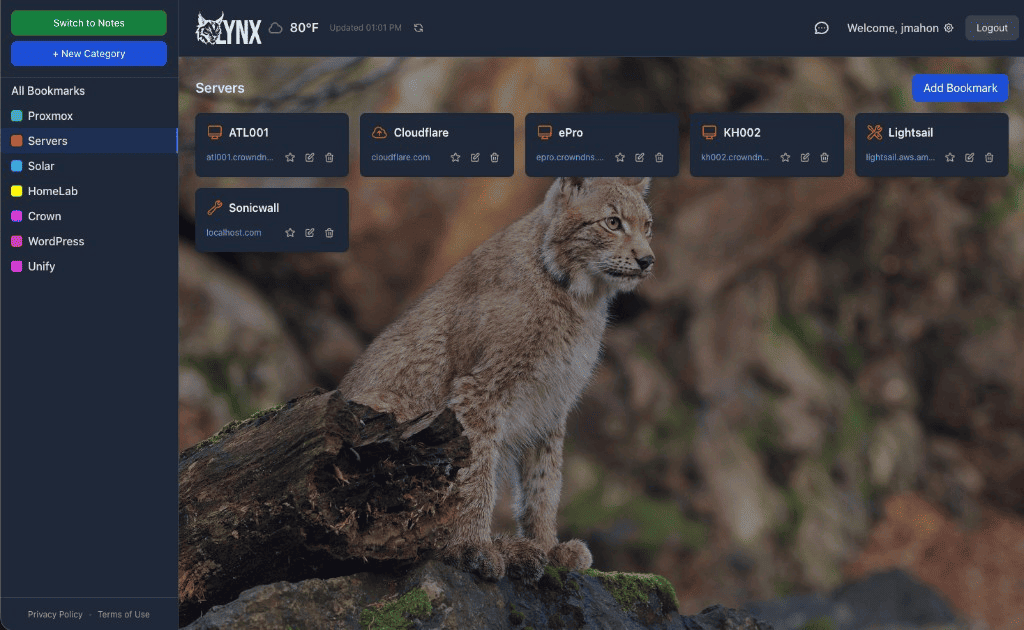
Practically, that meant pairing AI-generated tests with human-written abuse cases, validating disposal semantics under reload scenarios, and resisting shortcuts like “store ciphertext server-side for convenience” when the product promise explicitly says otherwise. The screenshot you see—categories such as Proxmox, Cloudflare, Solar—reflects real operator workflows: shared shortcuts for infra, not marketing fluff. AI helped us move faster toward that clarity; it did not define the threat model.
The takeaway
LYNX is free forever, deliberately priced to remove friction so teams can standardize on a secure hub instead of sprinkling credentials across consumer apps. That posture matches the product copy: privacy first, security by default, and features—bookmarks, notes, chat, weather, personalization—that respect both creativity and control.
If your roadmap looks like shared operational links plus sensitive coordination, put the workflow and the encryption model in the same place. Start at lynxdash.com—no credit card, no subscription—and build from a dashboard that treats your team’s everyday clicks and chats with the seriousness they deserve.